Ledger Login: Access Your Crypto Safely
Step-by-step guide to logging in, securing your device, and managing your crypto portfolio
Why Secure Ledger Login Matters
Ledger Login ensures your private keys never leave your hardware wallet, protecting your assets from phishing, malware, and unauthorized access. Unlike typical software wallets, Ledger Login requires physical confirmation on the device for every action, giving you full control and peace of mind.
Even beginners must treat login security seriously: a single mistake can lead to irreversible losses. Ledger Login combines simplicity with high-end security.
Core Terms
- PIN: Device-specific code
- Recovery Phrase: 24-word backup
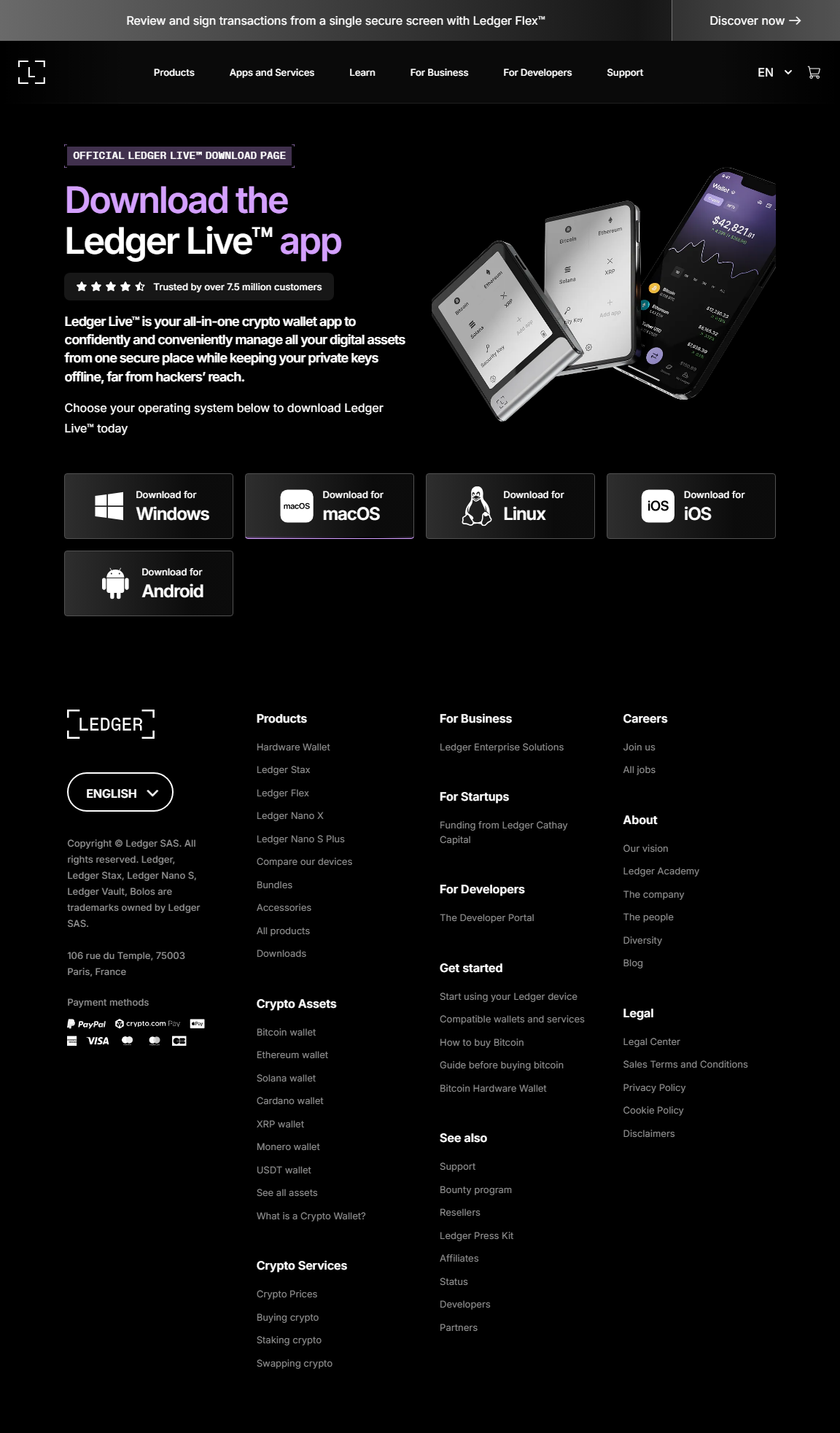
- Ledger Live: Official management app
- Private Key: Your proof of ownership
- Two-Factor Authentication: Optional extra security
Common Login Challenges
- Forgotten PIN
- Old firmware
- Phishing attempts
- Using unofficial Ledger Live versions
User Story: Sarah's Safe Login
Sarah almost entered her credentials on a fake site. By following Ledger Login correctly through Ledger Live and confirming her device physically, she avoided losing her crypto, demonstrating the importance of secure login practices.
Step-by-Step Ledger Login Guide
Step 1: Connect Your Ledger Device
Use a USB cable or Bluetooth (Nano X) to connect to your computer or mobile device. Always launch Ledger Live from official sources.
Step 2: Open Ledger Live and Initiate Login
In Ledger Live, select “Manager” or “Portfolio.” Ledger Login will prompt device verification before access.
Step 3: Enter Your PIN
Input your device PIN. Your private keys remain offline, ensuring secure login.
Step 4: Verify Device Authenticity
Ledger Live confirms the device is genuine and firmware is updated. Only verified devices can access your crypto portfolio.
Step 5: Enable Optional Security Features
Enable 2FA, notifications, and firmware updates to further enhance login security.
Ledger Login vs Software Wallets
| Feature | Ledger Login | Software Wallet |
|---|---|---|
| Security | Offline keys, physical verification | Online keys, phishing risk |
| Ease of Use | Moderate, requires device | Instant access, less secure |
| Recovery | 24-word seed phrase | Varies by app |
Trend Highlight: DeFi & Ledger Login
Ledger Login allows safe interaction with DeFi platforms. Your keys remain offline, even when lending, staking, or swapping crypto.
Login Best Practices
- Always download Ledger Live from official sources
- Never share your recovery phrase
- Keep firmware up-to-date
- Enable transaction alerts
Final Takeaway
Ledger Login is your first line of defense for cryptocurrency security. By following proper login procedures, verifying devices, and practicing good security habits, you ensure complete protection for your crypto portfolio.
Secure your login, verify your Ledger device, and confidently manage your digital assets.